De retour,
Sauvegardes faites.
1) Voici le rapport de Roguekiller :
RogueKiller V7.6.5 [03/08/2012] par Tigzy
mail: tigzyRK<at>gmail<dot>com
Remontees: http://www.sur-la-toile.com/discussion- ... ntees.html
Blog: http://tigzyrk.blogspot.com
Systeme d'exploitation: Windows 7 (6.1.7600 ) 32 bits version
Demarrage : Mode normal
Utilisateur: kicik [Droits d'admin]
Mode: Recherche -- Date: 06/08/2012 22:59:39
¤¤¤ Processus malicieux: 0 ¤¤¤
¤¤¤ Entrees de registre: 5 ¤¤¤
[HJ] HKLM\[...]\System : ConsentPromptBehaviorAdmin (0) -> FOUND
[HJ] HKLM\[...]\System : EnableLUA (0) -> FOUND
[ZeroAccess] HKCR\[...]\InprocServer32 : (C:\Users\kicik\AppData\Local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\n.) -> FOUND
[HJ] HKLM\[...]\NewStartPanel : {59031a47-3f72-44a7-89c5-5595fe6b30ee} (1) -> FOUND
[HJ] HKLM\[...]\NewStartPanel : {20D04FE0-3AEA-1069-A2D8-08002B30309D} (1) -> FOUND
¤¤¤ Fichiers / Dossiers particuliers: ¤¤¤
[ZeroAccess][FILE] @ : c:\windows\installer\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\@ --> FOUND
[ZeroAccess][FOLDER] U : c:\windows\installer\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\U --> FOUND
[ZeroAccess][FOLDER] L : c:\windows\installer\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\L --> FOUND
[ZeroAccess][FILE] @ : c:\users\kicik\appdata\local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\@ --> FOUND
[ZeroAccess][FOLDER] U : c:\users\kicik\appdata\local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\U --> FOUND
[ZeroAccess][FOLDER] L : c:\users\kicik\appdata\local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\L --> FOUND
¤¤¤ Driver: [CHARGE] ¤¤¤
¤¤¤ Infection : ZeroAccess|Root.MBR ¤¤¤
¤¤¤ Fichier HOSTS: ¤¤¤
192.168.1.10 kicik.fr
192.168.1.20 mail.kicik.fr
¤¤¤ MBR Verif: ¤¤¤
+++++ PhysicalDrive0: Hitachi HDT725032VLA360 ATA Device +++++
--- User ---
[MBR] 1ff550ad08691a7e1d94eb9fd30f362c
[BSP] e5ceb32d28cd94f50d817d9647d862a7 : Windows 7 MBR Code
Partition table:
0 - [ACTIVE] NTFS (0x07) [VISIBLE] Offset (sectors): 63 | Size: 277685 Mo
1 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 568700928 | Size: 27557 Mo
User = LL1 ... OK!
User = LL2 ... OK!
+++++ PhysicalDrive1: SAMSUNG HD103UJ ATA Device +++++
--- User ---
[MBR] 07ea87904c9987c3c1f0a5f7b8c54d26
[BSP] c18bc20f70d014c7f198c1560dd28ef6 : Windows 7 MBR Code
Partition table:
0 - [ACTIVE] NTFS (0x07) [VISIBLE] Offset (sectors): 2048 | Size: 100 Mo
1 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 206848 | Size: 953766 Mo
User = LL1 ... OK!
User = LL2 ... OK!
+++++ PhysicalDrive2: ST320002 1A USB Device +++++
--- User ---
[MBR] 2f3970186dc7707cf1bf304f54ca21db
[BSP] a2405411ca8b5c2ac36dbed5b0636aa3 : MaxSS MBR Code!
Partition table:
0 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 218137203 | Size: 937608 Mo
1 - [XXXXXX] UNKNOWN (0x74) [VISIBLE] Offset (sectors): 544370800 | Size: 937645 Mo
2 - [XXXXXX] LINUX-SWP (0x82) [VISIBLE] Offset (sectors): 225600882 | Size: 265696 Mo
3 - [XXXXXX] UNKNOWN (0x61) [VISIBLE] Offset (sectors): 2760638474 | Size: 25 Mo
User = LL1 ... OK!
Error reading LL2 MBR!
+++++ PhysicalDrive3: PI-239 USB 2.0 Drive USB Device +++++
--- User ---
[MBR] 4a58ea30070289308b4716ed69f1670b
[BSP] c72a129041a0e773a8b714ca80073440 : MBR Code unknown
Partition table:
0 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 63 | Size: 953867 Mo
User = LL1 ... OK!
Error reading LL2 MBR!
Termine : << RKreport[1].txt >>
RKreport[1].txt
2) Et voici le rapport de ZHPDIAG
http://cjoint.com/?0HgxlxFeS8Q
Sirefef R / P / AH
Section d'analyse de rapports et de désinfection : malwares en tous genre et autres indésirables. Demandes de nettoyage uniquement. Prise en charge restreinte : équipe spécialisée.
Modérateur: Modérateurs
Règles du forum
 Les désinfections sont prises en charge par un groupe spécifique, tout le monde ne peut pas intervenir pour désinfecter les machines (règles).
Les désinfections sont prises en charge par un groupe spécifique, tout le monde ne peut pas intervenir pour désinfecter les machines (règles).
 Les procédures sont sur-mesure, ne faites pas la même chose chez vous (explications).
Les procédures sont sur-mesure, ne faites pas la même chose chez vous (explications).
 Un topic par machine, chacun crée le sien.
Un topic par machine, chacun crée le sien. 
Re: Sirefef R / P / AH
![]() par Kicik » 06 Aoû 2012 22:12
par Kicik » 06 Aoû 2012 22:12
- Kicik
- Messages: 12
- Inscription: 06 Aoû 2012 07:20
Re: Sirefef R / P / AH
![]() par lenapache » 07 Aoû 2012 07:04
par lenapache » 07 Aoû 2012 07:04
Bonjour Kicik
Certaines variantes de ZeroAccess incluent un keylogger aussi par mesure de sécurité je te conseille de changer tous tes mots de passe une fois ce PC désinfecté.
Il reste encore pas mal de traces de ce dernier sur ton PC
Les rapports demandés doivent être postés en lien et dans la même réponse en utilisant cet hébergeur de fichiers
RogueKiller Suppression
Scan AdwCleaner
 Télécharge AdwCleaner ( d'Xplode ) Enregistre ce fichier sur le bureau et pas ailleurs
Télécharge AdwCleaner ( d'Xplode ) Enregistre ce fichier sur le bureau et pas ailleurs
Suppression avec ZHPFix
Le temps de téléchargement du script a été volontairement limité à 4 jours
Note : Tu as trois rapports à poster
Certaines variantes de ZeroAccess incluent un keylogger aussi par mesure de sécurité je te conseille de changer tous tes mots de passe une fois ce PC désinfecté.
Il reste encore pas mal de traces de ce dernier sur ton PC
Les rapports demandés doivent être postés en lien et dans la même réponse en utilisant cet hébergeur de fichiers

RogueKiller Suppression
- Lance RogueKiller.exe.
- Pour Vista et Seven fais un clic droit sur le fichier téléchargé et Exécuter en tant qu'administrateur
- Attends la fin du pré-scan
- Clique sur le bouton Scan ce dernier terminé clique sur Suppression
- Laisse l'outil travailler ne touche ni au clavier ni à la souris
- Un rapport (RKreport.txt) se créera à côté de l'exécutable, colle son contenu dans ta prochaine réponse
Scan AdwCleaner
 Télécharge AdwCleaner ( d'Xplode ) Enregistre ce fichier sur le bureau et pas ailleurs
Télécharge AdwCleaner ( d'Xplode ) Enregistre ce fichier sur le bureau et pas ailleurs- Double clique sur AdwCleaner.exe qui est sur le bureau.
- Pour Vista et Seven fais un clic droit sur le fichier téléchargé et Exécuter en tant qu'administrateur
- Clique sur Recherche
- Laisse l'outil travailler
- Le scan terminé, le bloc notes s'ouvrira avec le résultat du scan. Poste son contenu en lien dans ta prochaine réponse.
- Le rapport est également sauvegardé sous C:\AdwCleaner[R1].txt
Suppression avec ZHPFix
Le temps de téléchargement du script a été volontairement limité à 4 jours
- Clique sur Script ZHPFix
- Sur la page qui s'ouvre clic droit et Tout sélectionner
- Refais un clic droit et Copier
- Double clique sur
 qui est sur le bureau.
qui est sur le bureau. - Pour Vista et Seven fais un clic droit sur le raccourci de ZHPFix et Exécuter en tant qu'adminstrateur
- Clique maintenant sur
 (coller les lignes helper)
(coller les lignes helper) - Le texte copié dans le presse papiers s'affichera dans la fenêtre de ZHPFix
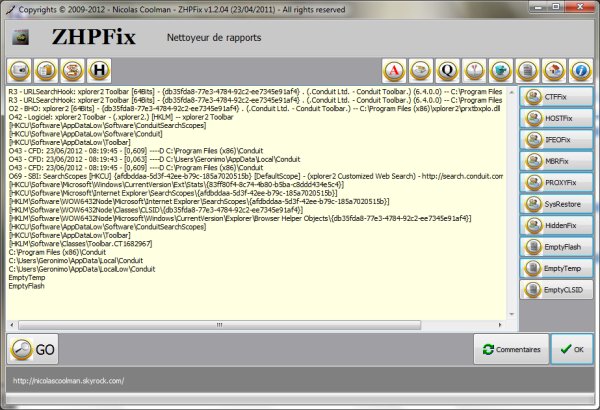
- Clique sur

- Confirme le nettoyage des données si demandé
- Patiente le temps du traitement
- Un rapport nommé ZHPFix[R*].txt sera créé et sauvegardé sur le bureau poste son contenu dans ta prochaine réponse
- Clique maintenant sur
- Ce rapport se trouve aussi ici D:\ZHP\ZHPFix[R*].txt
Note : Tu as trois rapports à poster
Granmére à poréte ale passe
-

lenapache - Super Libellulien

- Messages: 5728
- Inscription: 11 Sep 2011 11:32
- Localisation: Picardie
Re: Sirefef R / P / AH
![]() par Kicik » 07 Aoû 2012 07:47
par Kicik » 07 Aoû 2012 07:47
Bonjour,
Voici les 3 rapports.
1)Roguekiller
RogueKiller V7.6.5 [03/08/2012] par Tigzy
mail: tigzyRK<at>gmail<dot>com
Remontees: http://www.sur-la-toile.com/discussion- ... ntees.html
Blog: http://tigzyrk.blogspot.com
Systeme d'exploitation: Windows 7 (6.1.7600 ) 32 bits version
Demarrage : Mode normal
Utilisateur: kicik [Droits d'admin]
Mode: Recherche -- Date: 07/08/2012 08:24:11
¤¤¤ Processus malicieux: 0 ¤¤¤
¤¤¤ Entrees de registre: 5 ¤¤¤
[HJ] HKLM\[...]\System : ConsentPromptBehaviorAdmin (0) -> FOUND
[HJ] HKLM\[...]\System : EnableLUA (0) -> FOUND
[ZeroAccess] HKCR\[...]\InprocServer32 : (C:\Users\kicik\AppData\Local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\n.) -> FOUND
[HJ] HKLM\[...]\NewStartPanel : {59031a47-3f72-44a7-89c5-5595fe6b30ee} (1) -> FOUND
[HJ] HKLM\[...]\NewStartPanel : {20D04FE0-3AEA-1069-A2D8-08002B30309D} (1) -> FOUND
¤¤¤ Fichiers / Dossiers particuliers: ¤¤¤
[ZeroAccess][FILE] @ : c:\windows\installer\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\@ --> FOUND
[ZeroAccess][FOLDER] U : c:\windows\installer\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\U --> FOUND
[ZeroAccess][FOLDER] L : c:\windows\installer\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\L --> FOUND
[ZeroAccess][FILE] @ : c:\users\kicik\appdata\local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\@ --> FOUND
[ZeroAccess][FOLDER] U : c:\users\kicik\appdata\local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\U --> FOUND
[ZeroAccess][FOLDER] L : c:\users\kicik\appdata\local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\L --> FOUND
¤¤¤ Driver: [CHARGE] ¤¤¤
¤¤¤ Infection : ZeroAccess|Root.MBR ¤¤¤
¤¤¤ Fichier HOSTS: ¤¤¤
192.168.1.10 kicik.fr
192.168.1.20 mail.kicik.fr
¤¤¤ MBR Verif: ¤¤¤
+++++ PhysicalDrive0: Hitachi HDT725032VLA360 ATA Device +++++
--- User ---
[MBR] 1ff550ad08691a7e1d94eb9fd30f362c
[BSP] e5ceb32d28cd94f50d817d9647d862a7 : Windows 7 MBR Code
Partition table:
0 - [ACTIVE] NTFS (0x07) [VISIBLE] Offset (sectors): 63 | Size: 277685 Mo
1 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 568700928 | Size: 27557 Mo
User = LL1 ... OK!
User = LL2 ... OK!
+++++ PhysicalDrive1: SAMSUNG HD103UJ ATA Device +++++
--- User ---
[MBR] 07ea87904c9987c3c1f0a5f7b8c54d26
[BSP] c18bc20f70d014c7f198c1560dd28ef6 : Windows 7 MBR Code
Partition table:
0 - [ACTIVE] NTFS (0x07) [VISIBLE] Offset (sectors): 2048 | Size: 100 Mo
1 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 206848 | Size: 953766 Mo
User = LL1 ... OK!
User = LL2 ... OK!
+++++ PhysicalDrive2: ST320002 1A USB Device +++++
--- User ---
[MBR] 2f3970186dc7707cf1bf304f54ca21db
[BSP] a2405411ca8b5c2ac36dbed5b0636aa3 : MaxSS MBR Code!
Partition table:
0 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 218137203 | Size: 937608 Mo
1 - [XXXXXX] UNKNOWN (0x74) [VISIBLE] Offset (sectors): 544370800 | Size: 937645 Mo
2 - [XXXXXX] LINUX-SWP (0x82) [VISIBLE] Offset (sectors): 225600882 | Size: 265696 Mo
3 - [XXXXXX] UNKNOWN (0x61) [VISIBLE] Offset (sectors): 2760638474 | Size: 25 Mo
User = LL1 ... OK!
Error reading LL2 MBR!
+++++ PhysicalDrive3: PI-239 USB 2.0 Drive USB Device +++++
--- User ---
[MBR] 4a58ea30070289308b4716ed69f1670b
[BSP] c72a129041a0e773a8b714ca80073440 : MBR Code unknown
Partition table:
0 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 63 | Size: 953867 Mo
User = LL1 ... OK!
Error reading LL2 MBR!
Termine : << RKreport[2].txt >>
RKreport[1].txt ; RKreport[2].txt
2) AdwCleaner
http://cjoint.com/?0HhiTLjHtgJ
3) ZHPfix
http://cjoint.com/?0HhiUPmH7MQ
Voilà, merci et bonne analyse
Voici les 3 rapports.
1)Roguekiller
RogueKiller V7.6.5 [03/08/2012] par Tigzy
mail: tigzyRK<at>gmail<dot>com
Remontees: http://www.sur-la-toile.com/discussion- ... ntees.html
Blog: http://tigzyrk.blogspot.com
Systeme d'exploitation: Windows 7 (6.1.7600 ) 32 bits version
Demarrage : Mode normal
Utilisateur: kicik [Droits d'admin]
Mode: Recherche -- Date: 07/08/2012 08:24:11
¤¤¤ Processus malicieux: 0 ¤¤¤
¤¤¤ Entrees de registre: 5 ¤¤¤
[HJ] HKLM\[...]\System : ConsentPromptBehaviorAdmin (0) -> FOUND
[HJ] HKLM\[...]\System : EnableLUA (0) -> FOUND
[ZeroAccess] HKCR\[...]\InprocServer32 : (C:\Users\kicik\AppData\Local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\n.) -> FOUND
[HJ] HKLM\[...]\NewStartPanel : {59031a47-3f72-44a7-89c5-5595fe6b30ee} (1) -> FOUND
[HJ] HKLM\[...]\NewStartPanel : {20D04FE0-3AEA-1069-A2D8-08002B30309D} (1) -> FOUND
¤¤¤ Fichiers / Dossiers particuliers: ¤¤¤
[ZeroAccess][FILE] @ : c:\windows\installer\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\@ --> FOUND
[ZeroAccess][FOLDER] U : c:\windows\installer\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\U --> FOUND
[ZeroAccess][FOLDER] L : c:\windows\installer\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\L --> FOUND
[ZeroAccess][FILE] @ : c:\users\kicik\appdata\local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\@ --> FOUND
[ZeroAccess][FOLDER] U : c:\users\kicik\appdata\local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\U --> FOUND
[ZeroAccess][FOLDER] L : c:\users\kicik\appdata\local\{d8a0ba5a-29f7-2ba6-b226-3249ae4e939e}\L --> FOUND
¤¤¤ Driver: [CHARGE] ¤¤¤
¤¤¤ Infection : ZeroAccess|Root.MBR ¤¤¤
¤¤¤ Fichier HOSTS: ¤¤¤
192.168.1.10 kicik.fr
192.168.1.20 mail.kicik.fr
¤¤¤ MBR Verif: ¤¤¤
+++++ PhysicalDrive0: Hitachi HDT725032VLA360 ATA Device +++++
--- User ---
[MBR] 1ff550ad08691a7e1d94eb9fd30f362c
[BSP] e5ceb32d28cd94f50d817d9647d862a7 : Windows 7 MBR Code
Partition table:
0 - [ACTIVE] NTFS (0x07) [VISIBLE] Offset (sectors): 63 | Size: 277685 Mo
1 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 568700928 | Size: 27557 Mo
User = LL1 ... OK!
User = LL2 ... OK!
+++++ PhysicalDrive1: SAMSUNG HD103UJ ATA Device +++++
--- User ---
[MBR] 07ea87904c9987c3c1f0a5f7b8c54d26
[BSP] c18bc20f70d014c7f198c1560dd28ef6 : Windows 7 MBR Code
Partition table:
0 - [ACTIVE] NTFS (0x07) [VISIBLE] Offset (sectors): 2048 | Size: 100 Mo
1 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 206848 | Size: 953766 Mo
User = LL1 ... OK!
User = LL2 ... OK!
+++++ PhysicalDrive2: ST320002 1A USB Device +++++
--- User ---
[MBR] 2f3970186dc7707cf1bf304f54ca21db
[BSP] a2405411ca8b5c2ac36dbed5b0636aa3 : MaxSS MBR Code!
Partition table:
0 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 218137203 | Size: 937608 Mo
1 - [XXXXXX] UNKNOWN (0x74) [VISIBLE] Offset (sectors): 544370800 | Size: 937645 Mo
2 - [XXXXXX] LINUX-SWP (0x82) [VISIBLE] Offset (sectors): 225600882 | Size: 265696 Mo
3 - [XXXXXX] UNKNOWN (0x61) [VISIBLE] Offset (sectors): 2760638474 | Size: 25 Mo
User = LL1 ... OK!
Error reading LL2 MBR!
+++++ PhysicalDrive3: PI-239 USB 2.0 Drive USB Device +++++
--- User ---
[MBR] 4a58ea30070289308b4716ed69f1670b
[BSP] c72a129041a0e773a8b714ca80073440 : MBR Code unknown
Partition table:
0 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 63 | Size: 953867 Mo
User = LL1 ... OK!
Error reading LL2 MBR!
Termine : << RKreport[2].txt >>
RKreport[1].txt ; RKreport[2].txt
2) AdwCleaner
http://cjoint.com/?0HhiTLjHtgJ
3) ZHPfix
http://cjoint.com/?0HhiUPmH7MQ
Voilà, merci et bonne analyse
- Kicik
- Messages: 12
- Inscription: 06 Aoû 2012 07:20
Re: Sirefef R / P / AH
![]() par lenapache » 07 Aoû 2012 09:44
par lenapache » 07 Aoû 2012 09:44
Poste tous tes rapports en lien et limite la durée de téléchargement à quatre jours
As tu dans RogueKiller cliqué sur le bouton Suppression ? les instances du rootkit ZeroAccess n'ont pas été supprimée.
AdwCleaner Suppression
As tu dans RogueKiller cliqué sur le bouton Suppression ? les instances du rootkit ZeroAccess n'ont pas été supprimée.
AdwCleaner Suppression
- Double clique sur AdwCleaner.exe qui est sur le bureau.
- Pour Vista et Seven fais un clic droit sur le fichier téléchargé et Exécuter en tant qu'administrateur
Clique sur Suppression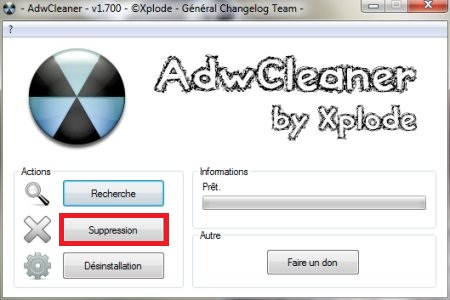
- Laisse l'outil travailler
- Le scan terminé, le bloc notes s'ouvrira avec le résultat du scan. Poste son contenu en lien dans ta prochaine réponse.
- Le rapport est également sauvegardé sous C:\AdwCleaner[S1].txt
Note : Tu as deux rapports à poster
Granmére à poréte ale passe
-

lenapache - Super Libellulien

- Messages: 5728
- Inscription: 11 Sep 2011 11:32
- Localisation: Picardie
24 messages
• Page 2 sur 2 • 1, 2
Qui est en ligne
Utilisateurs parcourant ce forum: Aucun utilisateur enregistré et 1 invité
- L’équipe du forum • Supprimer les cookies du forum • Heures au format UTC + 1 heure
Développé par phpBB® Forum Software © phpBB Group
Traduction par phpBB-fr.com

Traduction par phpBB-fr.com

phpBB Metro Theme by PixelGoose Studio


